
What is Spear Phishing
At this point in the technology era, most people are familiar with the term phishing. But there are still a lot of business owners and employees who are not familiar with it.
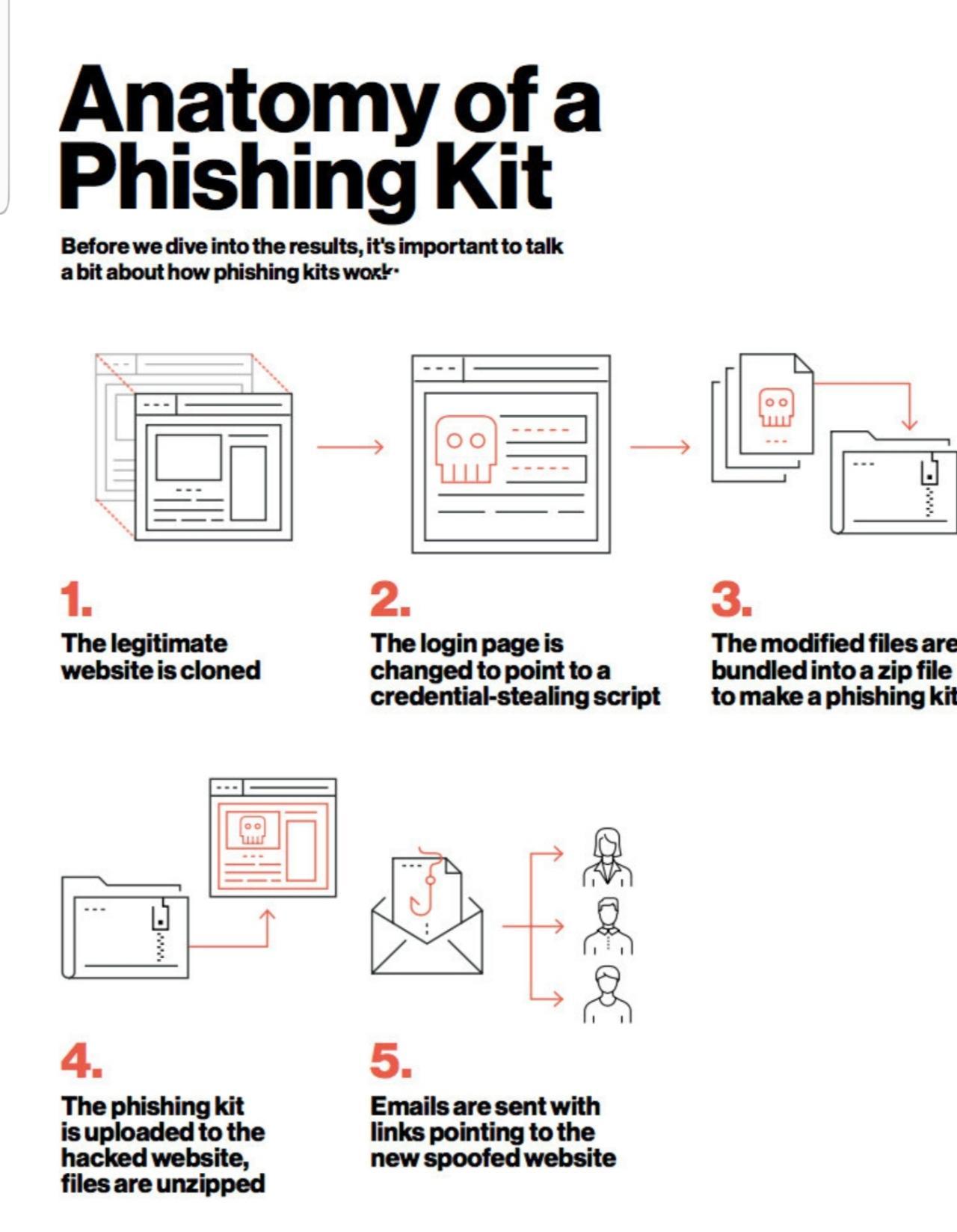
Phishing is the act of sending emails disguised as legitimate emails to get the recipient to do something they normally wouldn’t do. That action could be an attempt to at gaining access to a sensitive account (bank, PayPal, etc.) or to install malicious software (Ransomware).
Spear Phishing takes it a step further. Spear Phishing is the same as phishing except that it is a targeted attack, typically a C-level executive or someone specific.
Why is Spear Phishing a Big Problem?
I mentioned earlier that the two reasons attackers use phishing as an attack method are to gain access or to spread malware.
There has been a huge uptick in ransomware attacks in 2019 (more than double so far). Ransomware is a type of malware, a very dangerous type if your organization is not taking steps to mitigate it.
Ransomware encrypts your data and then demands a ransom to decrypt them. Even if you pay the ransom there is no guarantee that they will decrypt your files. Ransoms as of late have been in the hundreds of thousands of dollars.
The cost of lost productivity due to downtime has been much higher.
In almost all the recently well-publicized ransomware attacks the origin was email. It’s not clear if it was a spear-phishing attack but it is likely.
How Are Targets Identified?
The hacker methodology *simplified) is as follows:
- Reconnaissance & Information Gathering
- Social Engineering (Phishing)
- Attack
It’s not that hard to gather information in the technology age. A few internet searches and a couple of phone calls and anyone can identify potential targets.
A lot of the time email addresses along with names and titles are available on business websites. Even if they’re not it’s not difficult to get them.
Imagine this spear phishing scenario.
A hacker calls up a law firm and tells the person who answers the phone that they have an unpaid invoice for courier services. The hacker asks who he should send the invoice too.
We’ll call the person who answered the phone a receptionist. The receptionist says they should send the invoice to the office with attention to accounts payable.
The hacker says they would prefer to send it email because the payment is already late.
The receptionist obliges (it’s human nature to want to be helpful) and gives the hacker an email address for someone in accounts payable. The receptionist even puts the hacker through to the accounts payable voicemail.
The hacker leaves a voicemail for the accounts payable representative saying they are sending an invoice through email. He even states again that payment is late.
The accounts payable rep gets the email directed to them (spear phishing) and clicks on the link labeled invoice 1572 courier services.
This link downloads and installs ransomware onto the unsuspecting accounts payable rep’s computer. Even worse is the computer is mapped to the law firms file server. The file server is now encrypted crippling the law firm.
If proper mitigation is not in place the law firm is at the mercy of the hacker. They will also now have to report the attack and likely face fines.
This is a simple attack that included spear phishing.
Does it sound hard to conduct this type of attack?
Proper Education & Mitigation
 More than 80% of all businesses are actively receiving phishing emails. There are ways to mitigate phishing attacks. They include the following:
More than 80% of all businesses are actively receiving phishing emails. There are ways to mitigate phishing attacks. They include the following:
- Anti-Phishing as a service which includes automated phishing mitigation and human intervention
- Phishing education and training
- Phishing simulation to identify opportunities
- White-listing and/or black-listing email domains (though not always realistic)
- Business Continuity and Disaster Recovery
If steps are not taken to prevent an attack then it’s not a question of if, it’s a question of when.
Spear phishing and other types of phishing are growing in usage. A spear phishing attack has a higher rate of success because it’s personalized.
If you receive an email directed at no one specifically you’re more likely to ignore it. If an email is addressed to you personally, and you’re expecting it as in the case above, then you’re more likely to open it and act on it.
That’s why spear phishing attacks are more attractive to hackers. They have a higher success rate.
Other types of phishing you should also be aware of:

- Vishing-phishing through phone calls (voice)
- Smishing-phishing through SMS (text messaging)
- Phishing through social media (Facebook, LinkedIn, Twitter, etc.…)
In Conclusion
Ransomware is only going to get worse. Unpatched systems, under-protected businesses, and easily susceptible employees will continue to be targeted. If you believe your business cannot afford the proper phishing mitigation you should really start thinking about the cost of not having the right protection.
The most recent attacks have been in the hundreds of thousands of dollars just in ransoms. Factor in fines. lost productivity, and remediation and many attacks cost well into the millions. Can your business afford that?








Yikes, I hadn’t heard of this before. I hope it never happens to me. I would hate to lose millions.
This sounds awful. I dont have any other employees but I know that phising can happen to anyone.
I have heard of phishing but never spear phishing. This is truly terrible but it is good to know about it ahead of time in order to prevent it.
We definitely had quite a few phishing emails coming in where I worked. Sometimes it would be really obvious, but others I could see how someone who wasn’t diligent could open things they shouldn’t.
This is quite an eye opener and I am shocked at many revelations that you have done in your blog. Beautiful work. Keep it up.
This sounds terrible, I now about phishing and everyone could be a victim That’s why we need to be more secured on what w are doing online.
We’re talking A LOT about this at my company right now. Thanks for opening all of our eyes to this!
That’s a good thing! More companies need to do this.
Oh my gosh, I didn’t realize that people could do this. I’m going to share this with my sister who has her own business. Hopefully, it will save her small company from spear phishing.
I am speechless. I had no idea about this malware or the term sphishing. You have made me even more careful of what email I even open. Thanks for sharing!
This is definitely dangerous and I am wondering if modern accounting software is able to reduce this problem because many cloud-based accounting solutions come with the ability to send invoices directly to a generic email address which imports the data directly into accounts payable. It means that the company’s file server will not be impacted in any way.
This is a very good point. We use Intuit Quickbooks Online so all of our invoices are sent through them. I have however received emails claiming to be invoices (from companies I don’t even use). So the threat does exist.
My aunt who is in her 70s had her computer locked and told that she would have to pay to have it unlocked. If someone like her who only goes online to play FB games and read pottery magazines can have it happen, anyone can.
Unfortunately Facebook is a hotbed for this activity.
Thanks for sharing these details.I hope I will not be any victim of such scams.
Wow! I never heard the term spear phishing before but I can see why it is such a major problem. Scam artists are getting super savvy nowadays, it’s really scary!
I think we often forget that phishing can happen at work, not just through our personal email. You really do have to be vigilant and put best practices into place to avoid being hacked.
Great info on this. Phishing is just problematic across the board!
This is absolutely alarming for many businesses. I think understanding this deeper can make a lot of difference in terms of prevention. Be careful out there folks.
This is so scary. Thanks for sharing this info, even if it made me nervous! Great post Scott.